Keeping your data away from prying eyes becomes a lot easier with the best encryption software. Whether you need to hide top secret work documents or shameful videos from days past, it’s best to keep safe.
The best encryption software does more than just add passwords to your sensitive information. For starters, you'll want expert protection behind that password. Essentially, it's required that your software is built around 256-bit to keep intrudes away.
For the best of the best, additional security features are greatly appreciated. Secure file shredding is a must-have, essentially ensuring deleted files can never be recovered. Additionally, you'll also want an encryption software that doesn't take an age to complete.
The best encryption software can be difficult to pin down. Despite everything, the best option still comes down to your personal needs. With that said, take a look at our list below for some of our expert recommendations.
If you need extra security for your home computer, try out the best antivirus software, or look at getting a VPN service. For now, read on to find the best encryption software for you.
1. Secure IT: Best encryption software overall
Why you can trust Top Ten Reviews
Secure IT is inexpensive, comes with three user licenses and securely encrypts your data. That alone makes it one of the best value encryption software packages you can buy. It compresses files as it encrypts them making them three percent smaller. This makes them slightly easier to share in emails or save to USB drives, although it doesn't compress as well as some others we reviewed.
While it isn’t the fastest program we reviewed, Secure IT only took about 20 seconds to scramble our 63 test files. You can create self-extracting files, including those in EXE, RAR and ZIP formats, using Secure IT. These aren’t secure like encrypted files, but this feature makes it easy to compress less sensitive data, or share secured information with others that don’t have a deciphering program on their computer.
The program’s files shredder destroys any type of files. You choose the number of passes the files make through the shredder – the more passes they make, the less likely hackers are to find any track of the information. Secure IT is compatible with all versions of Windows, and works well with 10.
2. Concealer: Best encryption software for Mac

Concealer is designed specifically for Mac computers, and while it takes longer to encrypt files than other programs do, it compresses them as it encrypts to free up storage space on your computer.
This Mac encryption software performed well in our ease of use tests, and we were impressed with the number of file formats it can encrypt, including text files and tax forms. You can create categories and save encrypted files under them to keep your information organized. Also, you can customize and attach a card to each encrypted file so you know what it contains without decrypting it first. You have the option to secure the whole database with a master password, or you can secure each card file with its own unique pass key.
Because Concealer is a Mac program, it doesn’t have as many security features as those compatible with Windows. For example, it doesn’t have a file shredder or a password recovery option. It also doesn’t let you create less secure self-extracting files like EXE, RAR or ZIP. However, Concealer encrypts your files using the most secure 256-bit AES key and includes both a password generator and a strength meter, which helps you create passwords that are difficult for hackers to figure out.
3. Folder Lock: Best for extra features and tools
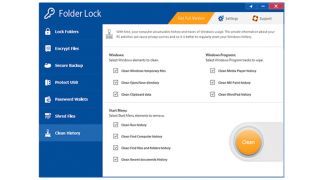
Folder Lock has some of the best security features and has plenty of tools to protect your sensitive information. It costs a bit more than other programs, but it also has a lot more features.
To encrypt files, you simply drag and drop them into Folder Lock, but you can also right click on the file you want to encrypt and see an option to secure it using Folder Lock. It took less than six seconds for the program to scramble our test files. While we only encrypted 128MB of data, it would only take a few minutes to secure several gigabytes. Once your files are encrypted, the program hides them so anyone who connects to your computer remotely or hacks into your system can’t see them. Also, Folder Lock uses the highest encryption algorithm available.
Folder Lock includes a file shredder, virtual keyboard and password strength meter, which helps you create strong passwords to your files. It is one of the only programs we reviewed that lets you recover your passwords if you forget or lose them – with other software, if you lose your password you lose your encrypted data.
4. SensiGuard: Most secure encryption software
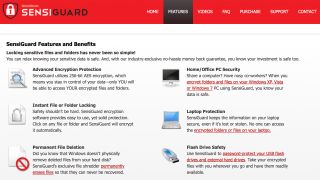
SensiGuard uses the most secure algorithm available to encrypt and secure your files, which means you're safe to send, share, or store with complete confidence. This software also includes a password strength meter and a secure file shredder, which are standard features among most encryption software. We like that you can secure files across your computer, laptop, and any external devices, offering encryption wherever you need it. It also compresses files too, which can save you space on your HDD or make files easier to share. However, there are some drawbacks.
SensiGuard is one of the more difficult programs to use, because it looks and feels very dated, and it takes longer than most encryption software to secure files. We also found it to have some issues with Windows 10, as its roots are in older versions of the Windows OS. It's a strong choice, but there are better options out there.
5. Renee File Protector: Best for password recovery

Renee File Protector’s best feature is it gives you a way to retrieve passwords that you have forgotten. In an age where you need a password for everything, and you're discouraged from reusing them, this is a god-send.
Most encryption programs exclude this option for the sake of security, but that also means if you forget your password you’re out of luck. Renee gives you the ability of setting up a password recovery option just in case. Plus, it tells you if a password you’ve chosen is a little too easy to figure out. You can hide encrypted files on your computer, so they can’t be seen by anyone who sees your computer, including hackers that sneak in. Unfortunately, Renee File Protector doesn’t compress files during the encryption process, which would save room on your storage drive. But it doesn’t bloat your files either.
6. AxCrypt

As far as encryption software goes, AxCrypt is a decent option for free and paying customers alike. Available on PC and Mac, the AES-256-bit key encryption provides users with expert security for their files. However, the free version only provides lesser 128-bit encryption.
While AxCrypt does have an incredibly confusing sign-up interface, the app itself is fairly straightforward. It will take a bit of digging to find some functions, but upon learning the ropes you'll soon find yourself whizzing through the UI.
Additional features aren't aplenty, but the expected ones are here. AxCrypt brings a fairly bog-standard file shredder for additional security, but also a fairly decent password manager to pick up the slack.
At just $3.75 a month, AxCrypt is one of the more affordable options on the market. Additionally, for those who don't want to spend, the software’s free option is still fantastic.
What do experts recommend about encryption software?
We consult with experts in the computer security industry as well as businesses that use encryption software daily, including those in healthcare, education and government industries. Their expert knowledge and experiences, as well as our own in-house tests, help us understand the many uses of encryption software, security levels and requirements, and the tools to look for when choosing a program.
One expert we spoke with is Marjorie Smith, a medical service software administrator for a Virginia-based company that assists doctors, hospitals and clinics with medical billing. Because personal medical information is communicated, both in-office and electronically, Smith and her team are bound by the Health Portability and Accountability Act, or HIPAA, laws and regulations.
Smith explained that HIPAA requires any information that is sent electronically regarding a patient must first be encrypted. Smith also explained that since IT personnel can connect to her computer remotely, files and documents stored on her computer must be encrypted.
One important feature Smith says is essential is a password recovery feature. Because HIPAA requires workers to change their passwords for programs used for storing or sending patient information several times a year, including encryption software, it’s easy to forget passwords. If you don’t have a good IT department at your disposal, which isn’t included with encryption software, a password reset feature is essential.
Can you encrypt an external hard drive?
You can encrypt an external drive, or thumb drive, using encryption software. The process is the same as if you’re encrypting files and documents on your computer. You have to select the data you want to encrypt and send it through your encryption software. You will be asked to set a password or keycode in order to unlock and decrypt the information in the future.
It is important to note that your external drives, including flash drives, must be encrypted separately from your computer. Just because you’ve encrypted your computer doesn’t mean connected external drives are encrypted as well. As with computer encryption, if you plan to share your encrypted files with a third party that doesn’t have the same encryption program installed as you do, make sure to choose encryption software that includes the option of use self-extracting files. This allows others to unlock secured files with a provided password without requiring an encryption program to be installed on their end first.
Some of the best external hard drives come with their own encryption built-in, though, so you may not need separate software if this is all you want.
What are the key features of encryption software?
Version Compatibility
If your computer runs an older version of Windows, such as 8, make sure the encryption program supports your operating system. On the flip side, you need to make sure you choose software that has changed with the times and supports the latest versions of Windows 10. Most support both the 32 and 64-bit versions.
While all the programs we tested are compatible with every version of Windows, we feel that SensiGuard is a good choice for older computers because it only has the most essential tools and won’t bog down your old PC. Plus, it is easy to move to a new computer if you choose to upgrade. However, it takes a while to encrypt and decrypt files.
If you have a Mac, you need a program that is designed specifically for that operating system – none of the programs we tested are compatible with both Windows and Mac machines. We believe Concealer is the best option for Macs.
Mac encryption software doesn’t have as many extra security features as Windows programs. They typically lack virtual keyboards, self-extracting file creators and password recovery tools. Mac programs also take a lot more time to secure files compared to Windows software.
Security
Encryption software uses different types of ciphers to scramble your data, and each has its own benefits. Advanced Encryption Standard, or 256-bit key AES, is used by the U.S. government, including the National Security Agency (NSA), and is one of the strongest ciphers available. It scrambles each bit of information. Blowfish and its newer version, Twofish, are encryption algorithms that use block ciphers – they scramble blocks of text or several bits of information at once rather than one bit at a time.
The main differences between these algorithms are performance and speed, and the average user won’t notice the difference. Blowfish and Twofish can’t encrypt large files, so if you need to secure gigabytes of data, use AES encryption. Blowfish and Twofish algorithms are considered practically unbreakable, though given enough time and computing power, both could theoretically be broken.
AES has long been recognized as the superior algorithm and is required for financial institutions, schools, government agencies and healthcare facilities that deal with sensitive personal information. Because of this we preferred programs that use it and ensured these were included in our final choice of the best encryption software.
You'll see older programs using 448-bit encryption too, which is still secure but only recommended for smaller files.
When Is a Free Program Enough?
Many free file encryption programs exist, and they might be strong enough for your needs. We tested VeraCrypt and Windows’ built-in encryption solution BitLock. These are bare-bones programs that allow you to protect your files and nothing else – they don’t have a file shredder, password generator or password strength meter. Also, these applications are less intuitive than their for-pay counterparts. The paid versions walk you through every step and have easy-to-read help files and tutorials.
So, if you’re comfortable and familiar working with certificates and keys to encrypt files, BitLocker may work well for you. VeraCrypt’s system encrypts in volumes and allows you to create a hidden, encrypted volume within another encrypted file.


