Best VPN service 2022: keep your data secure
The best VPN service is an essential part of a strong computer security setup

Having the best VPN service is an important safety tool that encrypts your internet traffic and sends it on a trip around the world, making it much harder, some would say impossible, for advertisers, scammers, hackers, and anyone who’s taking a little too much interest in things like your location and passwords to see what you’re doing.
VPN stands for virtual private network, and means you make a private, encrypted, connection across the very public network that is the internet. Among the things a good VPN can obfuscate is your geographical location, so you can access content that’s not usually available to you based on where you live. Foreign versions of Netflix, the BBC iPlayer for non-Brits, and US streaming services while you’re on vacation abroad suddenly come into reach.
Watch out for VPNs that won’t log your activity - known as ‘no-log’ services - as these are inherently more secure. A single button for turning them on and off is useful too, with a simple menu for switching locations and servers, as no one wants to fiddle with complicated interfaces when all they want to do is log into Netflix.
VPNs are a good choice if you’re worried about online security, but are only one part of a meshed approach to security that can also include the best antivirus software and the best internet security software too.
1. ExpressVPN: Best VPN service 2022
Why you can trust Top Ten Reviews
Specifications
Reasons to buy
Reasons to avoid
The best VPN service out there right now has to be ExpressVPN – and for many reasons. The easiest place to start is with just that, ease: the client (which comes on a host of devices, including iOS, Android, Mac, Windows, Linux and even BlackBerry) is really simple with a click-to-start option, but also offers deeper functionality if you need it. Either way, you'll be assured of excellent speeds across more than 3,000 servers in 94 countries, and superb security with enterprise-level encryption.
Other positives include DNS content unblocking and leak protection, P2P support, Bitcoin payment options, Netflix unblocking, a no logging policy, split-tunneling, a kill switch and 24 hours of live chat support every day of the week.
You can even use custom firmware to install this at the router level for some devices, meaning you'll be hidden by a VPN no matter which device connects to the Wi-Fi. You can even try all those features for free using the 30-day money back guarantee.
You can use this VPN service on five devices at any one time – some providers offer more than that. But since you can set ExpressVPN up on the router, to which any number of devices can connect. This is the best VPN out there right now. The price does reflect that level of service.
- Read our ExpressVPN review
2. IPVanish: Best VPN for P2P
Specifications
Reasons to buy
Reasons to avoid
If your main use for a VPN is to get torrents and P2P content, then IPVanish is one of the best VPN services for you. It boasts over 1,300 servers across more than 75 countries, which offer more than 40,000 shared IPs, unlimited P2P traffic and superb download speeds. As if all that didn't make you feel secure enough, the company owns and manages all of its own servers for another level of security.
Plus, you get 24/7 support, ten connections at once, and a seven-day money-back guarantee. So even though there isn't a free trial, you could always opt out within that time and spend nothing. Clients work on iOS, Android, Mac, Windows and even Fire TV and offer great features and options, with unblocking for Netflix and more as standard.
- Read our IPVanish review
3. Malwarebytes Privacy: Best VPN for online security

Specifications
Reasons to buy
Reasons to avoid
One of the biggest names in antivirus software, Malwarebytes is now offering its own VPN service in the form of Malwarebytes Privacy. As you might expect from a cybersecurity company, Malwarebytes Privacy focuses heavily on the security side of VPNs. It uses the WireGuard VPN protocol and 256-bit encryption to offer an exceptionally secure service. It’s also a no-log VPN, so it won’t track your network data either.
The app is easy to use and works across Windows, macOS, Android, and iOS devices so you can ensure that all your devices are connected. There are over 400 servers in 30+ countries, and our testing showed great speeds and reliable connections.
The downside of this focus on security is that some of the more fun uses of a VPN have suffered, namely using them with streaming services. Some of Malwarebytes Privacy’s servers work with streaming apps like Netflix, but it's hit and miss. If your main reason for owning a VPN is to watch foreign TV, then maybe look elsewhere. But if you want to stay safe and secure online, Malwarebytes Privacy is a great choice.
- Read our Malwarebytes Privacy review.
4. Hotspot Shield: Best free VPN

Specifications
Reasons to buy
Reasons to avoid
Hotspot Shield, as the name suggests, is a brilliant VPN for offering you personal protection when online. Specifically, this VPN service is excellent for browsing because it not only offers top security but also the company's own Catapult Hydra protocol. This is a superb system that makes sure you get the fastest download speeds possible and it really works, even when connected to servers that are really far from your real world location. This VPN service works on iOS, Android, Mac and Windows, but won't work on OpenVPN so you can't run it at router level unfortunately.
The service has two options, one is free to use but if you want most of the features you'll need to sign-up for full access and the best possible service.
Hotspot Shield has great features like five device connections at once, 24/7 support, over 2,500 servers in 70 countries and no ads. But you will struggle to unblock US Netflix and BBC iPlayer, which is a downer for some. That said, this VPN service does offer a free seven-day trial, so it may be worth giving it a go.
- Read our Hotspot Shield review
5. CyberGhost: Good all-rounder VPN
Specifications
Reasons to buy
Reasons to avoid
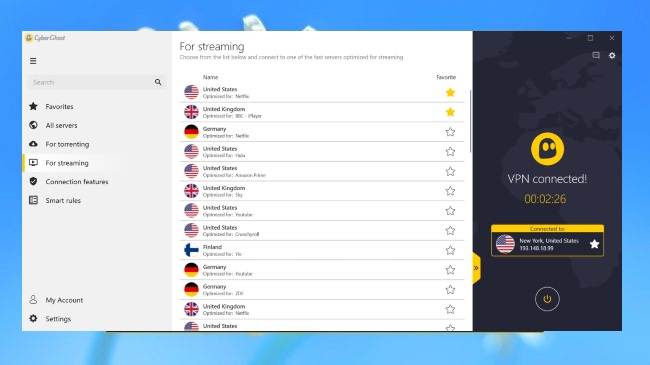
CyberGhost is a superb VPN service for deep-level personalization, making it an ideal choice for users who know what they're doing, know what they want, and know how to tweak the client to make it right for them. Since 2020 the servers are numbered at over 5,900 spread across over 90 countries offering excellent security and anonymity, and thanks to ad and malicious site blocking, automated HTTPS redirection and optional data compression, you can stay secure and keep your data use to a minimum.
A really nice feature is the ability to select the service you're using the VPN for and it will automatically find the best servers to suit the job. So you could select the likes of Netflix, YouTube, Hulu and more, and it will make sure geo restrictions are removed, so you can enjoy the content wherever you are in the world. The complex interface can be troublesome at times but, for all the aforementioned benefits, this very good VPN service is worth learning your way around. There's a stingy 24 hour free trial but then you get a 45-day money-back guarantee to enjoy.
- Read our CyberGhost review
6. Surfshark: Best VPN for beginners
Specifications
Reasons to buy
Reasons to avoid
While Surfshark is still a small fish in the VPN pond, it does offer over 800 servers across 69 locations, and supports Windows, Mac, iOS and Android as well as Chrome and Firefox. It offers URL and ad blocking, P2P support, VPN chaining, a kill switch, split tunnelling and zero-knowledge DNS servers for your privacy peace of mind. You also get 24/7 support, so even if you do have issues they can be quickly resolved.
While Surfshark isn't as cheap a VPN service as some, for most plans the two-year option does offer the best saving, and you can even pay using PayPal, cryptocurrency, Amazon Pay, Google Pay and Ali Pay, helping you remain anonymous. There's a seven day free trial and 30-day money-back guarantee.
A welcome ‘recently used servers’ tab makes regular access to the best servers for your needs nice and easy, a feature we really appreciated while we were testing Surfshark. All in all, if you're looking for speed, and put off by complicated menus and myriad options, Surfshark could be the best VPN service for you.
- Read our Surfshark review
7. NordVPN: A much improving VPN service

Specifications
Reasons to buy
Reasons to avoid
NordVPN is still one of the best VPN services when it comes to security thanks to a mind-boggling 2048-bit encryption, as well as not one but two kill switches, along with strong DNS leak protection. You can even pay with Bitcoin or Paypal to help add further anonymity to your experience. That all works across a whopping 5,600 servers spread over 60 countries, which we found to offer an above average speed performance.
The addition of the company's own SmartPlay service means you have a handy assistant for getting around geo-restricted content, meaning you can enjoy Netflix or Amazon Prime Video in whatever country you happen to find yourself.
A lack of live chat support may irk some, but we had very few problems – other than the odd server connection lag – so support shouldn't be needed anyway. And at the prices Nord offers, you should find this VPN service excellent value for money.
Note: NordVPN announced that it had a security breach at one of its many servers in March 2018. It maintains such as activity logs, usernames and passwords remained secure however some parts of some of its users' search history was potentially exposed. For that reason it has been bumped down from number two to number six in our list.
- Read our NordVPN review
8. KeepSolid VPN: Best VPN for Netflix
Specifications
Reasons to buy
Reasons to avoid
KeepSolid VPN Unlimited is great for unblocking the likes of Netflix or BBC iPlayer despite having just 400 servers. This is because they're well used, spread across over 80 locations worldwide. These are supported by a host of super secure protocols including OpenVPN, L2TP/IPSec, IKEv2, and PPTP but this also have the latest WireGuard too. There is torrent support but only via five locations, one being California though. Pricing is relatively low at $5 per month on a yearly subscription or $9.99 for a month at a time. Rarely, there is also a lifetime option for $199.99.
- Read our KeepSolid VPN review
9. TunnelBear: Best budget VPN service
Specifications
Reasons to buy
Reasons to avoid
Canada-based VPN service TunnelBear is a brilliantly easy-to-use VPN that doesn't only makes access simple, but also keeps security tight. It's one of those just-does-what-you-need type services that make life feel easier. As such, you are limited to just 1,000 servers across 20 location, and since long-distance connections did struggle in our tests, this may not be ideal for some (for example, if you’re an Aussie in the US trying to access a server Down Under). That said, connections work well, clients run across Windows, Mac, iOS and Android, plus you can set this VPN service up on a router.
We found that you can unblock the likes of US Netflix abroad, and the privacy policy is excellent, with the company hiring a private company to audit its server security. Speeds can be great and there's even a free VPN service for you to try with up to 500MB of free data per month.
- Read our TunnelBear review
10. Private Internet Access: Superb security VPN

Specifications
Reasons to buy
Reasons to avoid
Private Internet Access is a solid VPN that might not be the fastest - although still above average - but what it lacks in pace it makes up for in price and security. The servers are over 3,300 in number yet P2P is supported across all servers and you even get pro-level features like port forwarding and SOCKS5 support. There are clients for Mac, Windows, Android, iOS and Linux as well as good-looking browser extensions for Chrome, Firefox and Opera.
- Read our Private Internet Access review
11. StrongVPN: Good for multiple devices

Specifications
Reasons to buy
Reasons to avoid
StrongVPN rounds off our list of the best VPN services. It's not quite at the level of some in our guide – but it's better than most, thanks to its simplicity to use, support for a whopping 12 devices at once, and above-average performance speeds. Those speeds are helpful for streaming fans, as they works with the VPN's ability to unblock geo-restricted Netflix and BBC iPlayer content really easily. Clients are available for iOS, Android, Mac and Windows with router support and even Fire TV and Kodi compatibility.
The 950 servers might be minimal, compared to some, but they span 46 cities in 26 countries, and are backed by security in the form of L2TP, SSTP, OpenVPN, IPSec, and IKEv2 protocols. You can also rest easy knowing you get 24/7 customer support too. Pricing could be lower, but you do get a lot for your money with this VPN service.
- Read our StrongVPN review
How we test VPN services
We start by taking all the providers' plans and working our way into the depths of each individual VPN service from there. That means looking at value, features and pricing plans, as well as also privacy. This includes digging down into the terms and conditions to see how logging works to make sure security is as good as promised.
Performance is also another area we carefully look at in terms of download speeds, reliability, stability and variation across distances of servers. We also use IPLeak.net to check there are no privacy problems with the DNS. Of course, another factor is the client interface. This is tested in depth to make sure there are no annoying idiosyncrasies after you've committed to paying for the VPN service.
We then weigh up all these factors, assigning points to form an overall score, which helps us order each VPN service from best to least capable. Our final top ten list of the best VPN services right now are all excellent options, as any bad services have been assigned a lower score.
Best VPN services: how to choose the right one
There are a number of important factors to consider when you're choosing a VPN service to buy. Here are five pro tips for picking the right one.
1. Does the VPN service have servers in the countries and region you need? Consider which areas a VPN works in. While having more than one server in a country can help improve reliability, it doesn't guarantee improved performance. Don't assume that a plan with 500 servers will automatically beat another with 100.
2. How many simultaneous connections are supported? Normally this will be around three-five, so you can connect a desktop, mobile and tablet at the same time. Watch out though: a lot of VPN service providers specify that this is for a single user only, and have a fair usage policy to stop people using all the resources. .
3. VPN services do collect some data, despite not logging your online activities. Some record the day you logged on and the amount of data you used, and delete all other data at the end of the session. Other VPN services add items like your incoming IP address and server, and store that information for months. If that sounds alarming, you can find out more by checking the Privacy Policy and Terms of Service.
4. Do you need more features? Some clients display server load and ping time in the interface, helping you choose the right server. If you'll be using your VPN service a lot, you might want a "Favourites" system to save and recall specific servers. For experienced users, low-level network settings will help you customise the whole system.
5. Beware cheap deals. VPN deals can have all kinds of strings attached: restricted features; taxes excluded; the discount may only be valid for the first billing period only, automatically renewing to turn that $4.99/month into $10/month, so that apparent one-off $3.99 might become almost $10 next month. Read the small print, and ideally sign up with a service like PayPal where it's easy to cancel a subscription yourself if you need to.
6. Trial it. Found the best VPN service on paper? Give it a try before parting with a lot of cash. A short trial can only tell you a limited amount, so after that pay for a month, test the VPN as much as you can, and then upgrade to a better-value plan (a long plan, maybe yearly) if it still feels like the best VPN service for you.
Sign up to receive the latest news, reviews, buying guides and deals direct to your inbox
Luke is a veteran tech journalist with decades of experience covering everything from TVs, power tools, science and health tech to VPNs, space, gaming and cars. You may recognize him from appearances on plenty of news channels or have read his words which have been published in most tech titles over the years. In his spare time (of which he has little as a father of two) Luke likes yoga, surfing, meditation, DIY and consuming all the books, comics and movies he can find.

