Best internet security software: Protect your online devices
The best internet security software keeps your online life secure, and we've got collected all the best options to keep you safe

The very best internet security software could be the barrier between you and the deepest darkest depths of the internet finding their way into your life. Yes, life, not just device – as the two are so very closely enmeshed nowadays, making this software more valuable than ever before.
But how do you know which is best when it's difficult to even keep up with all the threats? One of the best places to start building a more robust defence system is with antivirus software. While that's a great way to fight viruses and malware, it's also worth considering tools like VPNs, password managers, banking protection and more.
Quite often you will find that when you pick a service it will come with a selection of package deals, so you may be best served going for your antivirus along with other protection tools, all from one provider. Or you may want to mix them up for the best of each, regardless of price.
From browsing the internet and online shopping to downloading files and banking digitally – there are lots of ways to be exposed both financially and in terms of personal privacy when you go online. As such it's worth considering tools that not only protect your devices – yup, smartphones as well as computers – but also protect your digital identity. Have that stolen and you can lose a lot and end up paying for it long after the fact.
So make sure you have the right protection even if you do own one of the best smartphones, best tablets, best laptops or best home computers – nothing is immune.
Some big names to look out for include the likes of Norton, McAfee and Bitdefender – but there are plenty of other options all varying in services and pricing. We've picked out a selection of nothing but the best options out there so whichever sounds like it's right for you, know that's it's been selected for quality over all others.
Bitdefender Total Security
Bitdefender Total Security has all the tools in Bitdefender’s basic internet security suite, including a password manager and parental controls. It even includes secure online storage for important files, so you can always be sure that your most crucial documents are in safe hands.
The right software isn’t just powerful, either – it’s versatile, too. Big-name products from companies like Bitdefender, Norton and McAfee are sold in different tiers. That means you can get the protection you need without paying over-the-odds for modules that you just won’t use – or, if you need a more robust solution, you can buy a premium product with additional features.
There are loads of great internet security software packages around, but so much choice can be confusing. We’ve done the hard yards so you don’t have to, though, by rounding up the top nine options and exploring their pros and cons – all you’ve got to do is pick the best product and get downloading. And for extra security, consider investing in the best antivirus software too.
Internet Security Software Explainer
Malware
Malware is a shortened name for malicious software. It’s an overarching term used to describe computer viruses, worms, trojan horses, adware, spyware and any other form of software that can harm your devices or steal your data.
Firewall
Firewalls are network security programs designed to monitor incoming and outgoing traffic on your devices, and to block malicious and unauthorized traffic. Most computers come with a built-in firewall these days, but the best internet security software will come with its own more powerful firewall.
VPN
VPN is an abbreviation for virtual private network. Using a VPN, you can encrypt your network signal and bounce it off a server anywhere in the world. This means that websites and other software can’t tell where your actual location is. This stops advertisers from targeting you with specific ads, but also stops hackers from getting into your network. You can also use a VPN to access region-locked content.
Best internet security software
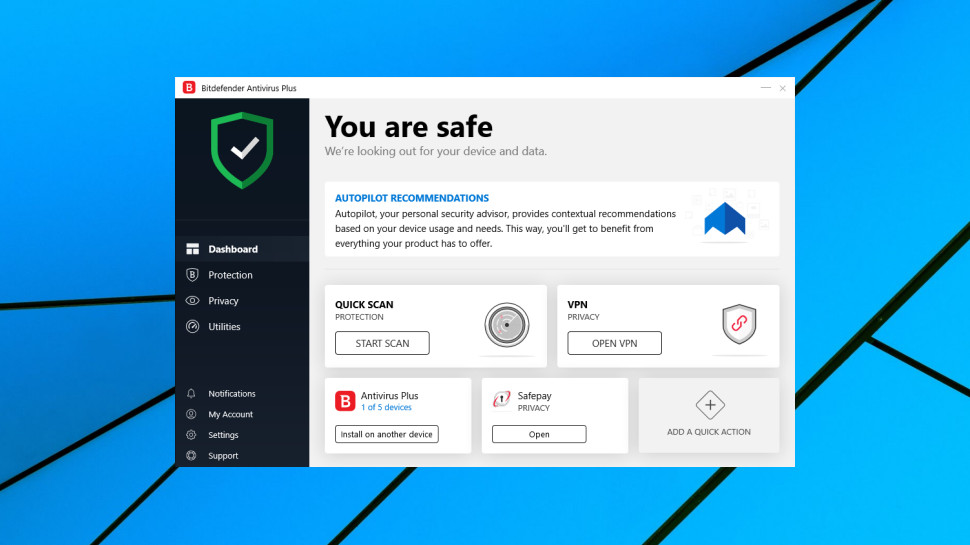
1. Bitdefender Total Security: Best internet security overall
Why you can trust Top Ten Reviews
Reasons to buy
Reasons to avoid
The Bitdefender name is now synonymous with internet security, and powerful protection at that.
Bitdefender has a Trustpilot score of 3.8 stars out of five with 69% of those reviews at the five star mark. One five star review said: "I have used several antivirus products over time and, for the past 3 years, Bitdefender. Product is reliable and very much "load and forget", (unless there is a security problem). Good to know it's there, in the background, quietly protecting devices." One negative review reads: "No matter how many times I have asked support, they can never fix their overzealous AV protection which blocks connections to all wifi outside of home, no matter how many exceptions I raise."
The company has built its reputation year after year by continuing to score highly in all the scores that matter when it comes to keeping you and your devices safe online. As such Bitdefender Total Security is a top pick and an ideal place to start for anyone new to internet security as well as a worthy upgrade for those more seasoned users.
There are several packages available meaning there should be something to suit most needs with a varying price structure that can help with budget ranges too. The basic plan – although the comprehensive tool list is anything but basic – is simply called Bitdefender Internet Security. This gets you sterling security but will be for your PC only and should you want wider device coverage you'll need to go up a plan level.
Protection offered, even at the most basic level, keeps you safe from malware, spyware, viruses and ransomware. You also have a firewall on top of all that to keep any of those nasties out of your machine from the outset.
As mentioned previously this scored well in testing, both with AV Test and AV Comparatives, where the experts are solely focused on how internet security software performs. In recent testing Bitdefender blocked nearly all viruses and malware that were fired at it.
Extra features include parental controls and a VPN for geo-restriction evasion. There's plenty more besides but it's worth weighing up budget with what you think you'll need – although you can rarely have too much security.
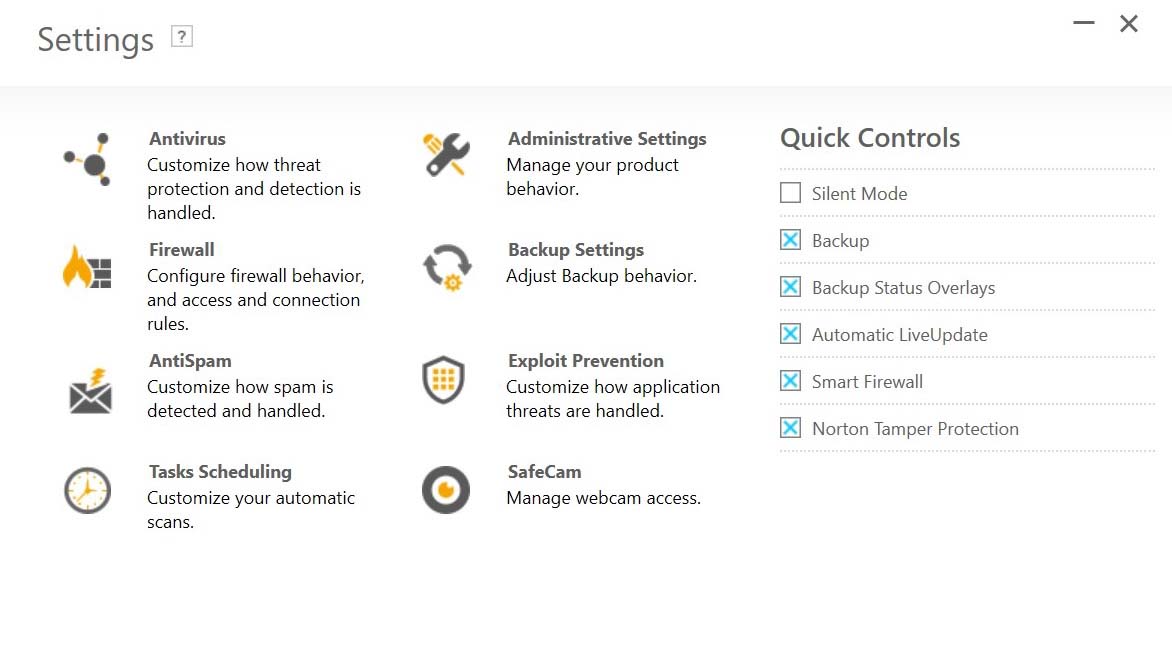
2. Norton 360: Best premium security

Reasons to buy
Reasons to avoid
Norton has been a huge name in the world of internet security pretty much since it all began.
Norton 360 has a Trustpilot user review score of 4 out of five stars with 50% at the five star mark. One positive review says: "Norton is THE best antivirus protection you can have, besides protecting your devices they also have the best customer support." A negative review read: "I stopped using the VPN in favor of another as Norton blocks even internet connectivity quite often (on multiple computers) and I'm one renewal away from making the jump to Malwarebytes as my only security software."
While that could mean sitting on its laurels, this brand has done anything but and is still leading the way when it comes to tackling the ever evolving threats that the internet houses. Norton 360 is the package which covers nearly all needs with varying levels of protection to suit each person's requirements.
At the base there is the Norton 360 Standard plan which, despite that name, offers more than enough security for most needs. Primarily you have the Norton Antivirus system which will keep infections off your machine. This will also work at fighting malware, spyware and ransomware which all threaten your digital identity and, as such, your finances.
This level also throws in a firewall which should mean hackers are kept at bay along with anyone else trying to access your device without permission. Unlike some other providers, Norton also throws in a VPN at this level which means you can hide your location or appear to be somewhere you are not - ideal for accessing your content when away from home.
Spend a bit more and the tiers increase the number of features to offer identity theft protection and financial coverage if you do succumb to identity fraud. At the top-end you even have coverage for unlimited devices and get 401k monitoring so your retirement is safe too.
All that and the performance of this software is tip-top, with expert testing finding this is able to block 100% of attacks – giving real peace of mind.
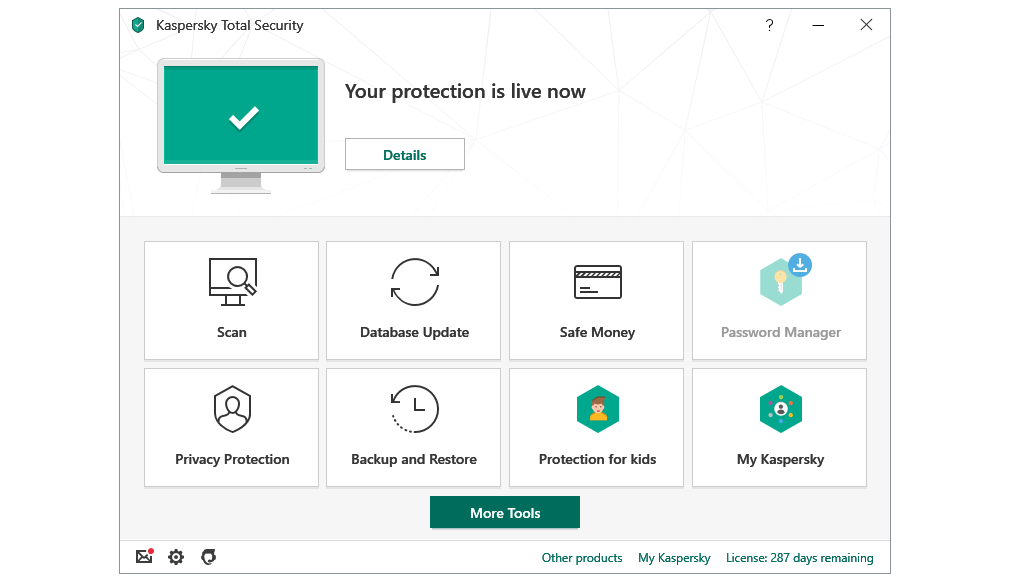
3. Kaspersky Internet Security: Best malware protection
Reasons to buy
Reasons to avoid
Kaspersky has gone from strength to strength in recent years and has firmly established itself as the name when it comes to blocking malware.
Kaspersky has a rating of 4.2 out of five stars on Trustpilot with 63% of those reviews being five stars. One positive review reads: "Excellent AV for my business and personal devices and from a trustworthy company." A negative review said: "Now it it is so awkward to renew, you can put an activation code in but nothing happens. You have to completely uninstall your old system and then download your new system."
While the other offerings on this list do offer impressive protection, it is Kaspersky that has a perfect track record, blocking 100% of malicious software under the expert testing of AV Test and AV Comparatives.
Like the other brands in this guide Kaspersky does break up its offerings into tiers which are priced at varying levels so as to suit the needs of most people, without breaking the bank.
Start at the base level and you will find the price of Kaspersky Internet Security very competitive even before you look into what that includes. Dig a little deeper and you'll see that gets you the company's flawless antivirus software to keep viruses, malware, spyware and ransomware totally at bay. You also get a firewall to keep out any threats that might try to hijack your device. Plus there is a VPN thrown in so you can spoof your location to keep hidden and add extra security when on public WiFi or abroad, for example.
But that's not all, this basic plan also gives you an ad blocker which means your internet browsing can be a far more minimalist experience without distractions to slow you down. It also means no more pop-ups or auto playing videos, which could save you on data when using your smartphone.
The top end package is Kaspersky Total Security which offers more premium features including parental controls – but thankfully even this level is reasonably priced comparatively.
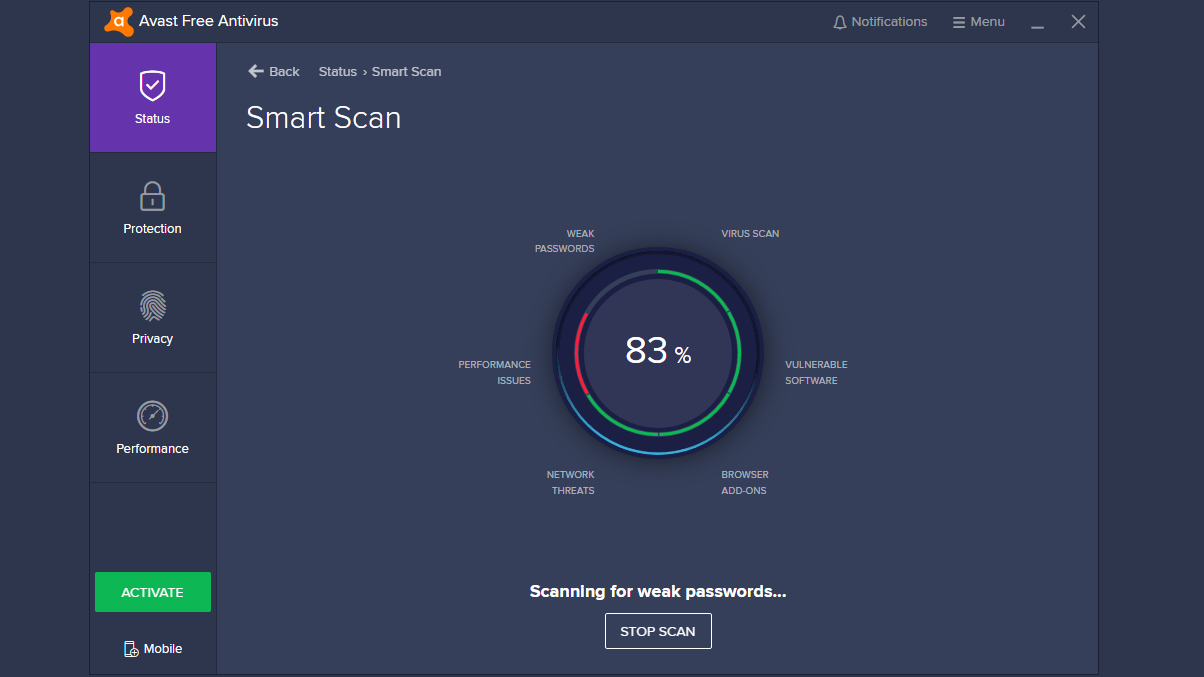
4. Avast Premium Security: Best for casual use

Reasons to buy
Reasons to avoid
Avast may sounds like a pirate cry, and leave you feeling that a jokey start for something as serious as security isn't ideal.
Avast gets a 3.9 out of five star rating over on Trustpilot where there is a 63% five star rating weighting. One positive review said: "I downloaded Avast Free, ran it, cleaned up all the unnecessary stuff and my computer is like new now! I'm so happy! Thank you." A negative review said: "The software is (like most antivirus software) little more than an ad-bot that sits around taking up resources and harassing you to buy product."
But in reality this company is able to joke as it is so secure in the knowledge that it offers premium and powerful protection against all the threats the interwebs can muster.
Unlike many other services Avast Premium Security also offers a free protection plan which is frankly the best free internet security system out there right now. That said, the premium paid for version, Avast Premium Security, isn't quite as impressive as the others higher up in this list.
Go for the free package and you get yourself a very capable antivirus software system which will battle any viruses, malware, spyware and ransomware that may attack. There's also a firewall as part of that offering to keep snoopers from getting into your device in any way. Rather uniquely this also offers a helpful sandbox feature which allows you to wall-off any area of your machine to open potentially threatening software without it being able to attack the rest of your device.
For anything else you'll need to upgrade to the paid-for plan. Go for the Avast Ultimate package and you're going to have a lot more powerful features at your fingertips. That includes a helpful VPN to mask your location, a password manager to keep you secure net-wide, webcam protection and a helpful file shredder.
Should you want parental protections you will be left wanting, which isn't great when you're paying for these features.
5. McAfee Total Protection: Best for technophobes

Reasons to buy
Reasons to avoid
McAfee is not only a big name in internet security but it's also one that aims to distill all its years of experience and prowess into a single offering.
McAfee rates poorly on Trustpilot with just a 1.3 star rating out of five. 84% of reviews are a one star rating. One positive review said: "Contacted support with a tech issue, their agent Hari was very polite, competent, and did a great job helping me out. you're a star!" A negative review read: "Be careful! Mcafee is very convenient to sign up for a subscription.. but if you want to stop it after the year subscription, the page does not load! I've lost quite a bit of money."
As such the McAfee Total Protection is a one-stop-shop solution that does it all – for more people – without overcomplicating it with different tier options.
That isn't to say this is totally fixed, as there is a variation in price based on the number of devices you want covered. But it's one system that applies to all, making this a super simple security pick for anyone new to this world or those that just want it easy.
Primarily this security protection is well tested and performs respectably. When it comes to antivirus and malware protection, McAfee was able to block a massive 97%. It's not perfect, like some of its rivals, but it's still impressive.
So this will keep you safe from malware, spyware, ransomware and viruses. And it will do all that with a simple solution. But if you want more then you may find the payment system frustrating. There is an option to get a VPN, to spoof your location, and also identity theft protection to keep you financially safe online. But to get access to those features you'll need to be paying for your software with an auto-renewal payment setup. Not everyone wants that level of commitment.
So if a simple one-stop-shop solution is what you need then this is a great pick but if you want a little more then it might be worth taking the time to consider the plans of other offerings.
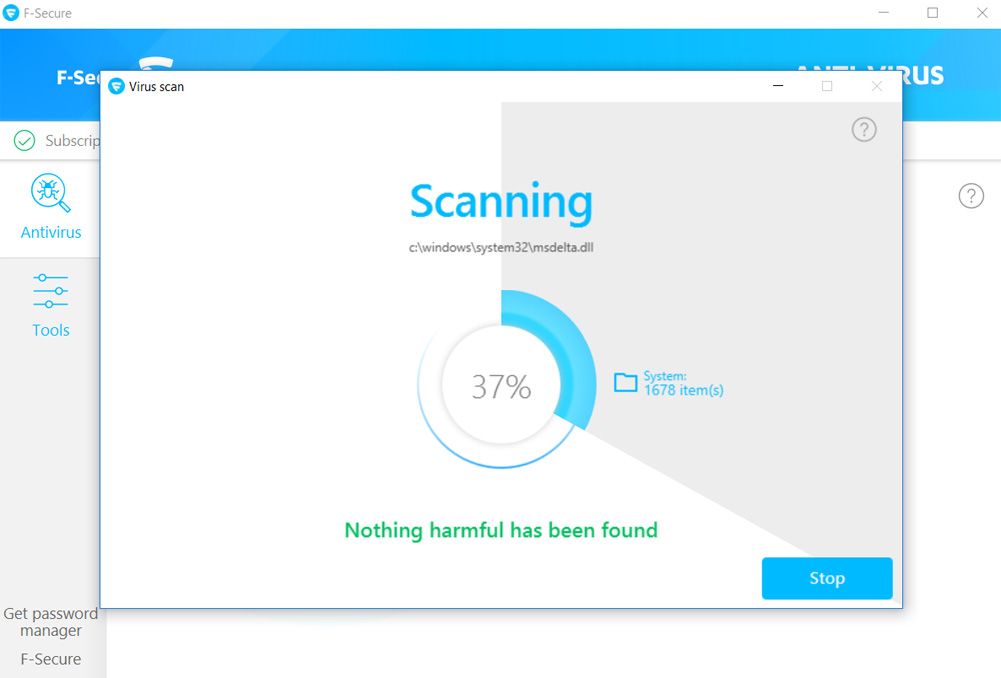
6. F-Secure Antivirus SAFE: Best for ease of use
Reasons to buy
Reasons to avoid
The F-Secure Antivirus SAFE software is the powerful yet simple to use antivirus protection program from a brand that is well known and respected. F-Secure has been around for many years where it has consistently done well in fighting threats online and protecting personal data.
The F-Secure Antivirus SAFE system is reviewed on Amazon with a 4.4 star rating out of five. That has 63% of reviews at the five star mark. One positive review reads: "Works quietly and efficiently in the background." A negative review says: "The price is too high when you look not only at the prices of superior competing products."
The antivirus software at the centre of this package is very much the star of the show as it is very powerful. That means this will repel viruses, malware, spyware and ransomware as well as phishing schemes and more. For all the features of other offerings this does the core – and arguably most important – work really well and without taking up too much of your system resources.
The package gives you multi-device coverage meaning you can have seamless protection running across your computers but also your mobile devices with iOS and Android specific protection offered here. Usefully this can also be used to help you find any device the software is installed on.
Misplace your smartphone or tablet? Use another device and you'll be able to locate it immediately. Of course this also applies if your smartphone gets stolen, making recovery a genuine possibility – helpful financially but also in terms of your data security.
Since the F-Secure Antivirus SAFE system keeps things simple it's a great choice for older machines that might otherwise struggle with some of the beefier solutions. It also means, on newer and more powerful machines, you're going to get the most energy and time efficient system protection without the bloat some others come with.
7. Trend Micro Antivirus Plus: Best for ransomware cover
Reasons to buy
Reasons to avoid
Trend Micro, a big name in PC security for years, goes beyond with the aptly named Trend Micro Antivirus Plus.
Trend Micro has a 2.4 out of five star rating on Trustpilot with just 23% at the five star mark. One positive review reads: "The first protection I've installed that doesn't bombard me with emails and pop ups trying to scare me into buying MORE extensions that I thought were part of the deal. They do what they say on the tin." A negative review says: "It flags safe programs as harmful, creates large undeletable junk files that at times take up 12 gigabyte and flat out stopped working before the expiration date."
That plus denotes that this is not a minimal product by any means and offers a robust selection of services which is built primarily on excellent malware protection.
If you want to avoid getting spyware, malware or ransomware on your machine – all of which can leverage your personal data against you – then this system is one of the most powerful and comprehensive ways to protect you. You even have anti spam and anti phishing protection meaning you can rest knowing you won't be bombarded by attempts to get into your machine – from any angle.
While this can be a little more resource intensive than other solutions – making it more for newer machines – this does offer broad protection. Plus you get a 30-day free trial so if you're not sure, you can always try before you buy to see how it works on your device.
One feature that stands out is the folder shield. This allows you to put enhanced protection on specific folders on your device, making it ideal for highly sensitive data which you might be responsible for.
There is a browser that is built specifically for fighting intrusions and you can have a booster for your firewall to make sure nobody can get into your device without your permission.
8. VIPRE Advanced Security: Best for minimal strain
Reasons to buy
Reasons to avoid
VIPRE Advanced Security comes from a company that is rated and used by the US military in some areas, which says a lot right from the outset.
VIPRE Advanced Security gets a 4.2 out of five star rating on ConsumerAffairs with lots of five star reviews. One positive review reads: "I have been using VIPRE for so many years I have lost count. When I needed support they were always prompt in their response. VIPRE is not a resource hog like some other programs. Great product. Thank you." A negative review says: "I have used VIPRE for my business for 3+ years. VIPRE recently renewed my membership without permission and have charged me three times the advertised price. I have attempted to call them numerous times with no answer."
It's been around for over 25 years, growing and changing as it has developed. But, despite being a heavyweight in its ability to fight attacks, it treads very lightly on your device.
This is thanks to a minimalist system which won't use lots of your device's resources to get the job done. That makes this a great pick for slower machines or anyone that wants their protection running in the background without their noticing.
Protection is real-time, with the software working to scan programs as they are in use, so that should mean if attacks happen, it can protect you immediately. That said, in testing this didn't score as well as some of the competition when it came to malware protection -- and phishing protection was poor. It's also worth noting that many of the firewall features are disabled by default. That said, the firewall does stealth ports and offers program control in a super easy to use way.
From the AV Test Institute the scores were the highest you can hit, putting this up there with the other big names in digital security. The same can be said for testing at AV Comparatives where, again, the highest score was achieved. So although the malware isn't the best, as mentioned above, this is not to be mistaken for a tool that isn't great as this is still one of the best you can get.
9. Webroot Secureanywhere: Uniquely light system

Reasons to buy
Reasons to avoid
Webroot Secureanywhere comes in low on this list but that isn't to say it's poorer than the others, simply that it is quite different.
Over on Trustpilot Webroot Secureanywhere has a 4.2 star rating out of five with a large 65% of that in five star reviews. One good review says: "I have been a Webroot customer for 15 years and still Webroot customer. I will recommend them to anyone. Webroot have an excellent software that protects our computer for any malicious threat." A negative review reads: "I frequently get emails stating that my Webroot subscription is about to expire when it's not, or is a subscription that I don't even have."
In fact this is pretty unique in the way it works. While most protection suites will be downloaded to your device and work as a software on the system to protect you, this offering works in the cloud.
Why would you want to use the cloud when all the others use software on the machine? Because this uses an advanced artificially intelligent brain to do the thinking. So while traditional systems need to quickly spot a threat and stop it before damage can be done to your device, Webroot Secureanywhere works backwards at its own pace.
If a threat is detected the AI brain will assess and make sure it is a problem, once it's decided that it is, everything will simply be rolled back to just before the incursion took place. All that means the strain on your system is minimal with just a 2MB file, compared to 700MB on most others. So that makes this great for older and slower devices.
Since this works uniquely it is also difficult to assess properly. As such the test results are mixed with a few very impressive scores but also some noticeable issues that are worth keeping in mind. But should you be worried, the company is aware of this, since it's relatively new, and offers a peace of mind trial. You can try out Webroot Secureanywhere for a massive 70-days during which time you can get all of your money back whenever you want, guaranteed.
Buying advice for the best internet security software
Why trust us on internet security software?
We’ve researched all the packages on this list to compare their features and pricing. We’ve also analyzed results from several important third-party testing labs, including AV-Comparatives and AV-Test, to see how each application handles a selection of threats and how efficient they are in terms of computing resources.
This approach allows us to see how each application performs over an extended period with a wide variety of threats, and it also means we can see what each package is like in day-to-day use – after all, it’s no good if the software performs well, but it’s got a complicated or awkward interface.
What is the difference between antivirus software and an internet security suite?
A top-quality antivirus package will protect your systems from viruses, malware, trojan horse applications and other similar threats. Many antivirus packages also protect you from ransomware and phishing attempts.
Internet security suites include all those features, but they also provide extra tools that deliver a broader range of benefits. You’ll typically find firewalls, VPNs, parental controls, identity theft prevention and online banking protections in internet security suites.
Internet security suites don’t just come with additional features. They’re usually sold with more licenses, too – you can typically install the software on more devices. That makes a full suite a better choice for families and ideal if you want to protect phones alongside PCs and laptops.
One other difference between basic antivirus software and internet security suites is the number of user licenses you get. Most antivirus solutions come with a single license to protect one computer. Internet security suites, however, usually come with at least three licenses, and are sometimes compatible with mobile phones and tablets so you can protect multiple web-enabled devices at once.
What should internet security software come with?
Internet security is a multifaceted system which should come with several tools in order to give you the full protection that is needed online. That said, the core of most systems is the most important part and if all others were forsaken this would still do a good job of keeping you safe. That is the antivirus software.
A decent antivirus program will protect you from viruses, malware, spyware, ransomware and in some cases phishing attacks too. By keeping these threats at bay -- at least spotting them if they get in -- the system is able to ensure further infection to your device is stopped. That, in turn means keeping your personal details, and finances, safe.
But it is also worth thinking about other powerful tools like a firewall -- although many machines already have these built in. But a strong one can mean a layer to keep threats at bay and ensure individuals can't get into your data.
A VPN is also worth considering as this will mask your IP address by running it through another server somewhere else in the world. That means keeping you private and hidden, ideal for security and worth using if on unsecured WiFi like at a coffee shop or airport. But it also means you can access content that might otherwise block you with geo restrictions. Want to get your local shows while abroad? You can appear at home by using your VPN and still get them. This can also be great for banking.
Password managers are also very helpful tools as these can generate strong passwords for you to use and save them for you. This means you have different passwords for everything you use, increasing the security should one be compromised -- keeping everything else out of reach.
Parental controls can work well for anyone that wants to limit their kids' access to certain websites that may be potentially threatening. But these are also helpful for seeing what your kid is up to -- ideal for tackling potential cyberbullying.
How much does an internet security program cost?
Internet security packages offer more functionality than antivirus software, so they do typically cost more. If you want a year’s worth of protection from one of the big names then you should budget for at least $40 or $50, and some of the top packages cost twice as much.
There’s plenty of wiggle room here too, though. You’ll often find discounts available for new users, and prices become more cost-effective if you purchase a multi-year deal. Conversely, packages with more features or with licenses for extra devices cost extra.
Happily, big companies do tend to make it easy to compare products and features, so you can see what’s available in each product. That makes it simpler for users to find out what they need – so they can avoid paying over-the-odds for protective software.
Sign up to receive the latest news, reviews, buying guides and deals direct to your inbox
Ian Stokes is the Tech Editor here at Top Ten Reviews. He has extensive experience in tech and games journalism, with work published on IGN, Kotaku UK, Waypoint, GamesRadar, Trusted Reviews, and many more. You'll find him covering everything from smartphones and home computers to 3D printers and headphones. He's also our resident cocktail expert.