Best antivirus software: Stay safe online with premium and free software
The best antivirus software will keep your personal electronic devices safe from a variety of threats.

Sign up to receive the latest news, reviews, buying guides and deals direct to your inbox
You are now subscribed
Your newsletter sign-up was successful
The best antivirus software is important to stop any viruses or other threats from infecting your PC. A lot of people use their computers to handle finances, medical records or other sensitive things so it is more important than ever to be protected. Some viruses can steal your passwords and personal information - this can lead to financial loss, and can slow down your PC or stop it from working altogether.
With the best antivirus software, you don't have to worry about the best home computers becoming infected. They can also be used to protect the best smartphones and the best tablets, with some even offering plans that can cover multiple devices so that you can keep the best laptops protected too.
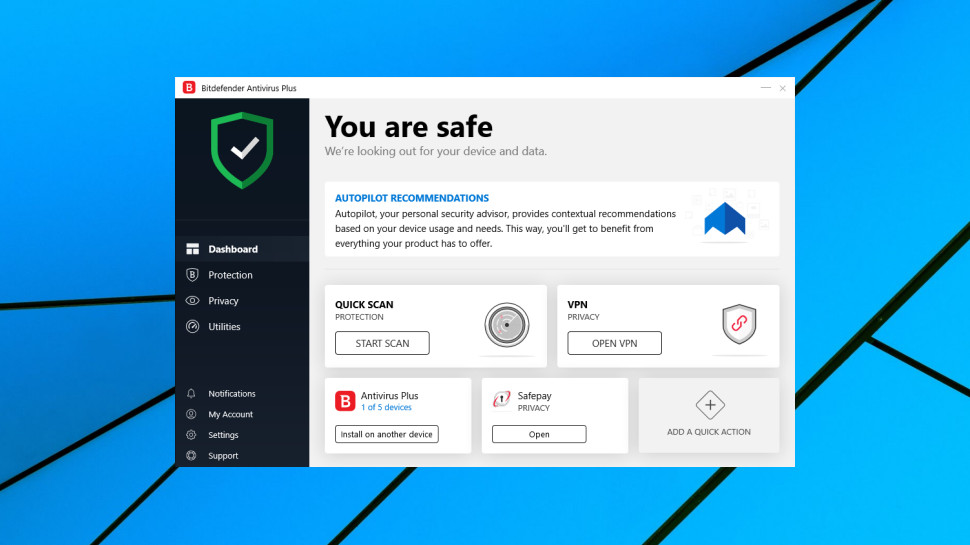
Bitdefender Antivirus Plus is the best antivirus software right now. It delivers watertight security, has excellent extra features, and it's very easy to use. With the basic antivirus package, Bitdefender Antivirus Plus you get protection against viruses, spyware and ransomware. It's extremely good value for money, too!
A good quality antivirus will protect a number of devices, whether it's your personal computer or your smartphone. Company's are often monitoring and logging the most recent threats so that any new viruses can be stopped in their tracks before they have a chance to infect your device - much like physical viruses, computer viruses are constantly evolving and changing, with new threats emerging every day.
Some of the best antivirus software utilize AI (artificial intelligence) to monitor your PC and react almost instantly to any unusual changes. Once it is installed on your device you can browse the web without worrying about your personal information being leaked.
The majority of antivirus tools are available as an annual or monthly subscription, with many of them offering different tiers to cover different needs, budgets and devices. This means if you only need to cover one device, you have the option to save money by going for a more basic package without sacrificing any security. If you don't want to spend any money, then there are some free options that can offer a decent level of protection.
You might also want to consider the best internet security software for more all-around protection. These will offer antivirus software while also including VPNs, firewalls and password management/encryption.
Antivirus software explainer
Malware
Malware is short for malicious software, and it's a catch-all term to cover various types of threats that your device faces, including viruses, worms, trojan horses, spyware, adware etc.
Firewall
A firewall is a network security device on your computer that monitors incoming and outgoing network traffic, and blocks unauthorized or dangerous traffic. Windows and Mac computers have built-in firewalls, but many antivirus programs come with their own firewall program too.
VPN
VPN stands for virtual private network. These programs offer you a way to stay anonymous online, by encrypting your network signal and bouncing it off another server. This prevents websites from knowing where you are. They can also be used to access content that is region-locked. Some antivirus and internet security programs come with VPN access included.
Best antivirus software
Specifications
Reasons to buy
Reasons to avoid
It was definitely close but we believe BitDefender is the best antivirus software on the market. With the basic antivirus package, BitDefender Antivirus Plus, you get protection against many different types of viruses, including spyware, ransomware, trojans, worms and any new threats that may emerge. You can get plans for home use or for your business so that you can keep your family and company files safe. If you need antivirus for your business, BitDefender also offer a number of other cyber security features which can help to keep you and your employees safe - they can even help to keep Microsoft Office documents and Google Cloud safe and secure.
BitDefender has a number of positive user reviews on Best Buy with an average rating of 4.5 stars out of 5. Users praise its ability to give great overall protection to devices, with viruses being blocked and eliminated before they have a chance to infect your laptop or computer. The small number of negative reviews are surrounding complications with buying through a third-party retailer, with people dissatisfied that they have to go to Best Buy for customer support rather than BitDefender themselves.
BitDefender has been tried and tested and blocked between 99.5% and 100% of malware attacks set against it when tested by white hat industry experts - they have the testing to back up their claims.
The software also includes a VPN alongside its impressive antivirus software. VPNs are a great way to browse the internet anonymously so that you can't be tracked by corporations, your ISP, or individuals with malicious intentions. Paired with good antivirus software, VPNs will allow you to browse the internet with complete confidence.
BitDefender has a Safe Files feature which will encrypt and safeguard important files further so that they are extra safe in the rare case when something damaging slips through the cracks. Costs start at $19.99 for the first year of cover, which is really a great price when you consider the features and protection that you get.
- Read the Bitdefender Antivirus Plus review.

Specifications
Reasons to buy
Reasons to avoid
Coming in a close second on our list, Norton 360 Antivirus Plus only misses the top spot by a hair. You get a highly effective, highly protective antivirus software suite that protects you against a multitude of virus types, including ransomware, spyware, trojans, worms and file infectors. Much like BitDefender, Norton backs up their claims with excellent results in industry tests from AVTest and AV-Comparatives where Norton 360 scored perfect marks in the most recent round of testing, with almost every single infection being stopped in its tracks and eliminated effectively.
Norton 360 Antivirus Plus has a number of positive reviews on Amazon with an average rating of 4/5 stars. Users praise how easy it is to install, with even the least tech-savvy users having no problem setting it up on their devices. Some of the negative reviews are dissatisfied with the subscription renewal system, as it can cost more after the current subscription expires.
Norton 360 Antivirus Plus also includes a password manager and 2GB of online cloud storage, which you can utilize to store your most sensitive and vulnerable files that could otherwise be corrupted or stolen if your home computer is infected or compromised.
Norton 360 Antivirus Plus offers protection for Windows PCs, Macs, smartphones and tablets. Some of the more expensive subscriptions allow you to protect multiple devices at once, with the most expensive option offering protection on 10 devices simultaneously.
The PC cloud backup varies in size from 2GB to 100GB depending on the subscription that you choose, but we would not recommend buying a more expensive option purely for the cloud storage as there are a number of free options such as Google Drive and Dropbox which do the same thing without costing any extra money. Subscriptions that offer multiple device protection also feature parental controls and school timers, so that you can keep your children safe from inappropriate content.
- Read the Norton 360 Antivirus Plus review

3. AVG Ultimate
Reasons to buy
Reasons to avoid
AVG Ultimate is an all-in-one antivirus, tune-up, anti-tracker and internet filter that can be used across multiple devices. When we tested AVG Ultimate, we found that the antivirus and anti-tracker elements to be great tools, as they will intercept and block any potentially harmful cookies or malware before they get a chance to gather any information from your PC.
AVG Ultimate has very favorable reviews on Amazon with an average rating of 4.5 stars out of 5. Users praise its ability to stop threats before they have a chance to infect your PC and will catch any that slip through the cracks with thorough virus scans. The small number of negative reviews appear to mainly be from people who had trouble setting up the software, which is an issue that can be easily avoided by watching a tutorial or following a guide.
AVG will also scan every download and installation so that your devices are safe from any unwanted software or viruses, stopping them before they have a chance to infect your device. In addition to the preventative measures, AVG will automatically do regular virus scans on your device.
AVG Ultimate does have an internet filter, but it's not as novice-friendly as the others on the list. If you are a tech-savvy individual, AVG's internet filter offers uncapped potential when it comes to blocking websites, as the sites have to be added manually rather than by category.
To the experienced tech user, this could be seen as a positive, as it offers uncapped filtering potential. However, for those that are less experienced, it can be tough to block large amounts of websites in a time-efficient manner. This is the main downside that we found while testing the product.
During our testing process, we found AVG to be a great all-around set of internet security tools, and an ideal choice if you want a thorough anti-virus.

Specifications
Reasons to buy
Reasons to avoid
What would you say if we told you that one of the best antivirus softwares on the market costs absolutely nothing? Nada, zilch, bupkis. Well it’s true, because Avast Free Antivirus is, as the name suggests, completely free. There are no hidden fees or delayed costs. It’s just free.
But surely it can’t be as good as the other antivirus programs out there, right? Wrong. Avast Free Antivirus offers you the same levels of protection as many of the other big names in the field, covering your devices from attacks by viruses, spyware and various other forms of malware. It performs excellently too, blocking between 99.7 and 100% of attacks levied at it by experts during their latest rounds of testing.
The downside is that it doesn’t run as efficiently as some premium antivirus software, so you may experience noticeable slowdown on your computer, especially if you’re using an older device. A small price to pay, when you’re not paying any price at all though.
- Read the Avast Free Antivirus review

Specifications
Reasons to buy
Reasons to avoid
While other companies have tiered their offerings, McAfee only offers a single antivirus solution called McAfee Total Protection. This is more of a full blown internet security software in truth, but it does include antivirus protection so we’d be remiss not to mention it here.
When it comes to antivirus protection, McAfee has been one of the big names for years now and it still offers a great product, though some of the competition might have started to pull away. The antivirus stood up to between 97.8 and 98.4 % of attacks in the most recent round of expert tests, which is excellent, but falls short of some of the other antivirus programs on our list.
You get a ton of other features rolled into the package, including a firewall, password manager, file shredder, and a secure VPN. But these aren’t freebies or extras, they’re part of the security package that you’re paying for. Pieces start at $29.99 for single device coverage for a year. That’s not bad, but if you just need an antivirus program you can get more devices covered for cheaper elsewhere.
- Read the McAfee Total Protection review
Specifications
Reasons to buy
Reasons to avoid
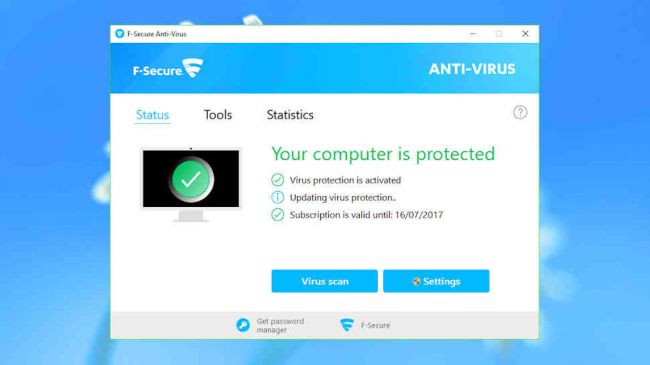
F-Secure Antivirus SAFE is quite the serious piece of antivirus software. It comes with fantastic additional features to keep your system secure, such as banking protection for safe online shopping, and safety tools to protect your entire family, including time limits and content blocking. This protection extends beyond your desktop computer, too, with a device finder that can help you track down a lost Android or iOS device - and remotely lock or wipe it too, to keep data safe.
F-Secure Antivirus SAFE delivers premium antivirus protection, receiving high marks after testing by major labs, including AV-test. It’s worth pointing out that some noted more false positives were generated than other antivirus software packages, but whether that affects you will depend on how you use your computer.
We like that this antivirus software program runs lightly - making it ideal for an older system. Another pro is the clean, easy-to-use interface. F-Secure Antivirus SAFE is an impressive package, and well-deserving of a place in our best antivirus software guide.
- Read the F-Secure SAFE review.

Specifications
Reasons to buy
Reasons to avoid
Trend Micro Antivirus+ Security delivers highly effective protection. The antivirus software scores particularly well for anti spam, and comes with an effective ‘Folder Shield’ module to block ransomware. It has a reputation for being easy to use too.
Although the best testing labs agree that its protection is very good, there’s some inconsistency to the details. AV-Comparatives, for example, reports a comparatively high number of false positives; while AV-Test found very high accuracy and no issues with false positives. One issue some agree on though is that Trend Micro Antivirus+ Security may be more resource intensive than others, making this antivirus software better suited to newer, more powerful systems.
We didn’t notice any performance problems, however. We found protection levels to be similar to Bitdefender, false positives were only marginally higher, and it didn’t slow down our system noticeably more than anything else.
Happily, there’s a free 30-day trial – which we’d advise running to check how the program performs on your system. If there are no noticeable issues, Trend Micro Antivirus+ Security is one of the best antivirus software programs you can choose.
- Read the Trend Micro Antivirus+ Security review.
Reasons to buy
Reasons to avoid
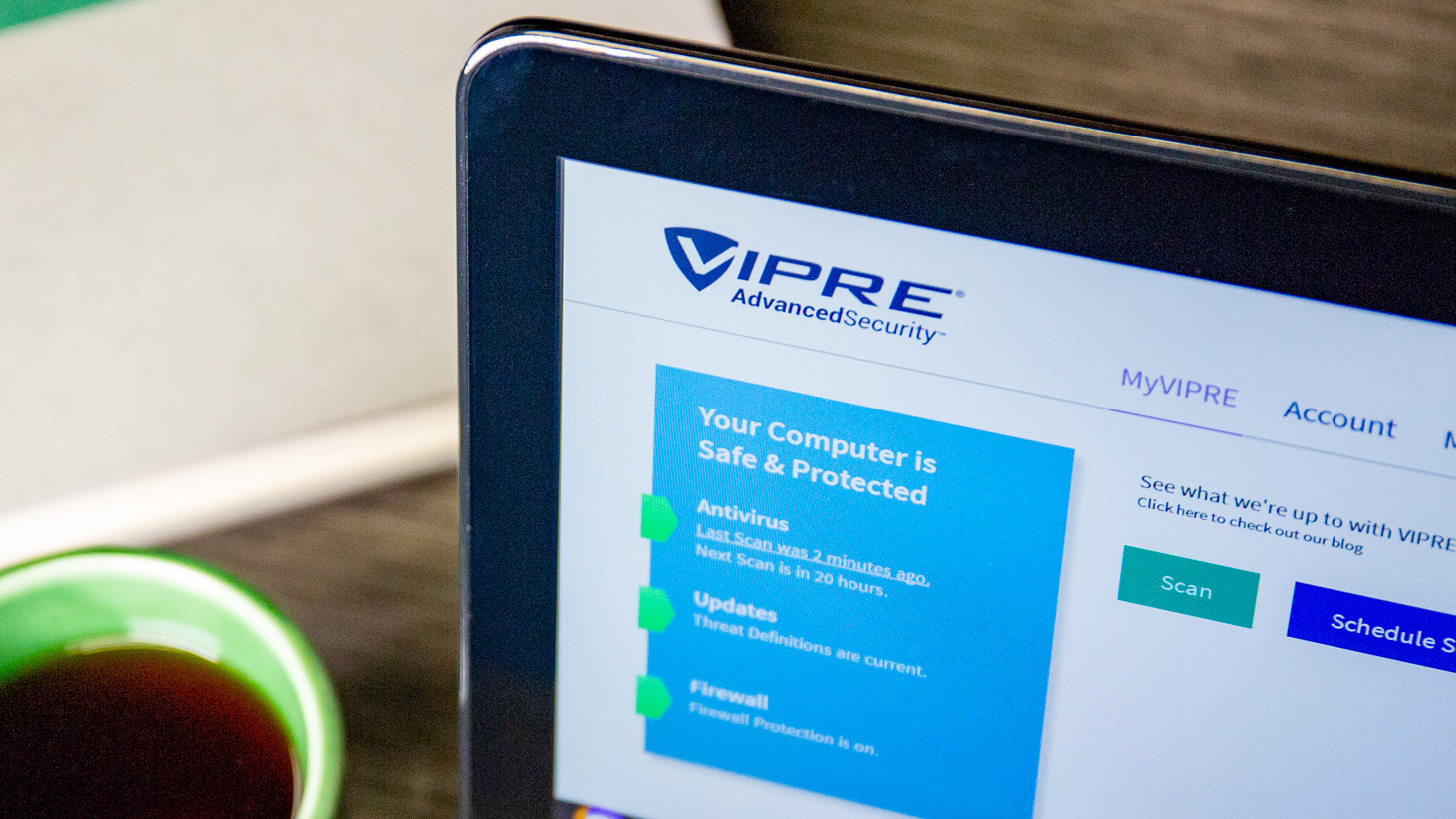
VIPRE Advanced Security is the easiest antivirus software program to install and use among the antivirus programs we tested. It’s easy to find the tools, functions and folders you need because they are clearly marked with large icons and big text.
Subfolders and tools, like the quarantine folder and custom scan settings, are in the main folders where you would expect them to be, so it’s not hard to navigate this program. Also, setting up VIPRE doesn’t take a lot of guesswork, and it doesn’t cause much slowdown of your computer while its running, even during deep virus scans.
While third-party test laboratories don’t test VIPRE very often, we checked out how well it protects against malware and were happy to see it blocked 99 percent of the over-300 live malware samples we used for testing.
- Read the review: VIPRE Advanced Security

Specifications
Reasons to buy
Reasons to avoid
If you’re looking for a truly lightweight tool, Webroot SecureAnywhere AntiVirus is the best antivirus software you can choose. Sure, most other products claim to be lightweight, but Webroot SecureAnywhere AntiVirus is the only one to really live up to the claim: it’s tiny – and it’s exceptionally fast.
It takes just seconds to install, and the program files are barely 2MB in size (some antivirus software can more than 700MB), with no bulky signature updates to hog your bandwidth. But just because it’s light on space, it doesn’t mean Webroot SecureAnywhere AntiVirus is light on features. Aside from the core protection, it comes with smart behaviour monitoring, accurate real-time antiphishing, a firewall and network connection monitor, enhanced anti-ransomware, and other bonus features.
The top testing labs don’t evaluate Webroot's products very often, so it’s tough to directly compare this program’s accuracy with that of the other best antivirus software programs. But when they are tested, they score well - and certainly our tests revealed solid, reliable protection.
The company is so confident you’ll like it, Webroot has given SecureAnywhere AntiVirus a generous 70-day 100 per cent money-back guarantee. If you’re fed up of bloated engines, Webroot SecureAnywhere AntiVirus is a very good product and worth a shot.
- Read the review: Webroot SecureAnywhere Antivirus
10. Norton 360 Deluxe
Reasons to buy
Reasons to avoid
Norton 360 Deluxe is the big brother of Norton 360 Antivirus Plus. It offers one of the best antiviruses on the market, while also giving you several other security features.
With this subscription, you get a secure VPN, which will anonymize you online and allow you to browse with complete security without the worry of being tracked by corporations, governments, or your ISP. Norton will give you a good deal on your first year, with prices often up to 75% off for first-time customers.
Norton 360 Deluxe also offers Dark Web Monitoring. If your personal details are stolen or leaked and appear on the Dark Web, Norton will inform you so that you can change passwords or email addresses to keep your sensitive information and logins safe.
One of the features that really stand out to us is the password manager. When you sign up to a website or service, Norton will generate a super strong password and automatically save it so that you can make note of it or use it automatically when you log into a specific site. This is much better than using the same password for every site, as your entire online presence may be compromised if one of them gets leaked. You also get SafeCam, a feature that alerts you if someone attempts to access your webcam and helps you to block future unauthorized access to it.
With this particular subscription, we would only recommend spending the extra money if you really think it is worth it. If you don't see yourself utilizing the extra features then we would recommend Norton 360 Antivirus Plus or one of the other more basic options on our list.
How we tested the best antivirus software
We’ve thoroughly researched antivirus software from all the big names in internet security, including Norton, McAfee, and Bitdefender. We’ve spent hours finding out what each antivirus software offers and how much they cost and discovered how they perform in real-world situations.
We turn to industry experts and in-depth laboratories when deciding our overall antivirus ratings, and with good reason – these facilities test for malware, zero-day threats, false positives, and other security issues.
X-HEAD: Can antivirus software remove existing viruses?
It can be challenging for any antivirus software to find and eliminate threats that were already on your system – because lots of viruses and malware applications block detection or mimic legitimate applications.
Ultimately, antivirus applications will remove some existing malware, but not all of it. And these apps can’t usually repair existing damage.
If your PC is already infected, we recommend that you seek professional help – computer stores and local experts will be able to remove malware and get your PC fighting fit.
Once your PC has been thoroughly cleaned, you should install an antivirus package to ensure that you don’t end up in the same situation again.
Antivirus software FAQs
Can antivirus software remove existing viruses?
Why you can trust Top Ten Reviews
It can be challenging for any antivirus software to find and eliminate threats that were already on your system – because lots of viruses and malware applications block detection or mimic legitimate applications.
Ultimately, antivirus applications will remove some existing malware, but not all of it. And these apps can’t usually repair existing damage.
If your PC is already infected, we recommend that you seek professional help – computer stores and local experts will be able to remove malware and get your PC fighting fit.
Once your PC has been thoroughly cleaned, you should install an antivirus package to ensure that you don’t end up in the same situation again.
How much does good antivirus software cost?
Mainstream antivirus packages don’t tend to be expensive. The top utilities generally cost between $20 and $50 per year, but prices vary between brands. Prices change elsewhere, too: you’ll often get a discount if you buy a multi-year package, but you may also have to pay more if you want to protect multiple devices.
If you want to save cash, many antivirus software companies have introductory discounts, and you can switch to a different provider the next year to take advantage of another deal. And, at the other end of the scale, expect to pay more if you want additional features.
Companies like Avast, Avira and AVG produce free antivirus software. They don’t have the features of paid products and they’re usually ad-supported, but they will certainly protect your PC.
Using your data to help others
Bitdefender Antivirus Plus 2020 also has a data sharing program that allows the software to send information about viruses, Trojans, rootkits and other malware found on your computer back to its databases. This is a way to keep tabs on new threats and pass along protection to other Bitdefender users before the malware becomes a cyber outbreak.
There hasn’t been any evidence of Bitdefender gathering inappropriate or unauthorized information, so we’re confident Bitdefender is safe to use. However, you can turn off this feature altogether from the Bitdefender dashboard if it worries you.
What is the best mobile antivirus software?
Most smartphone operating systems have built-in antivirus software alongside loads of other security features, but you can also deploy third-party applications if you’d like an extra layer of protection.
Bear in mind, though, that most basic and entry-level antivirus applications don’t cover smartphones. If you want smartphone protection, you’ll need to purchase a more comprehensive package, like McAfee Total Protection or Norton 360 Standard. Those products tend to cover PCs, laptops, and smartphones for one price.
What is the best antivirus for business?
We found that Kaspersky is the best antivirus choice for small businesses, with superb malware protection alongside straightforward design – it’s easy to use even if you’re not experienced with technology. Kaspersky also uses cloud computing to keep its apps updated, which is ideal if you don’t have an in-house IT team.
Kaspersky’s small business software covers up to 50 users, so it’s well-suited to protecting all devices in more compact organizations – and it covers smartphones and tablets as well as PCs and laptops. As well as antiviral protection, it includes password managers, backup tools, anti-spam and anti-phishing modules and web controls.
We’d also highlight Avast’s business products for larger firms. There are various products that can protect up to 100 or 1000 devices, and the packages include firewall and VPN modules for added security. Avast’s products also have a vulnerability scanner, so you’ll get alerts about potential threats before they’re exploited, and it can even monitor employee webcams.
Do I need to uninstall an old antivirus program before installing a new one?
Most antivirus software competes with other protection programs, so you need to uninstall your old program before installing a new one. Also, antivirus programs take up substantial memory, and having two installed will cause your computer to run much slower. During the installation process, most programs perform a scan to see if any other antivirus software or components are already installed, and they will either uninstall the old program for you or prompt you to uninstall it manually.
However, there are a couple programs that work in tandem with other antivirus software. Both AVG and Avast work alongside other protection software to add a second layer of security, catching threats your main program may miss. In both programs, you can turn off the virus detection and scan features – your main program can provide those specific service, and you can still take advantage of AVG’s and Avast’s more advanced tools like safe banking and password managers.
If you install Avast or AVG as a secondary antivirus program, make sure to install it after your main antivirus. Otherwise, your primary program will require you to uninstall it before completing the installation process.
What is a personal firewall?
Firewalls should form a critical part of any security setup – because they inspect your internet traffic and block harmful content. Firewalls are included in modern operating systems, in routers, and in antivirus packages and security software.
Many operating system and router firewalls are not infallible, though, because they don’t check inside packets of information for hidden threats – so malware can still creep through.
Firewalls from leading security companies do tend to look inside these packets, though, so they do a better job of spotting tricky threats. If you want to be truly secure, it pays to use a third-party firewall that can better identify and eliminate potential problems.
Sign up to receive the latest news, reviews, buying guides and deals direct to your inbox
Ian Stokes is the Tech Editor here at Top Ten Reviews. He has extensive experience in tech and games journalism, with work published on IGN, Kotaku UK, Waypoint, GamesRadar, Trusted Reviews, and many more. You'll find him covering everything from smartphones and home computers to 3D printers and headphones. He's also our resident cocktail expert.
- Monib ZahdehTTR Staff Writer
- Mike Jennings